Increase Pen Test Frequency & Coverage
Go Beyond Vulnerability Assessments And Validate Risks & Security Controls By Conducting Safe Attacks
Go Beyond Vulnerability Assessments And Validate Risks & Security Controls By Conducting Safe Attacks
Consider a new asset is added today or a new critical CVE is published, will you wait for your next Pentest to uncover it and fix it?
Organizations employ Pentesting to validate critical risks and assess the potential impact of a critical CVE. Traditional Pentesting, guided by human experts and following a step-by-step waterfall model, typically covers only 10 to 20% of assets in each assessment. In contrast, Continuous Pentesting offers an Agile and Automated approach that can cover 100% of assets in a single round and responds rapidly to newly added assets or published CVEs.
Our Automated Pentest platform gives you multi-stage attack playbooks to mimic a real attacker and accurately pinpoint prioritized vulnerabilities that would be targeted first. Automated Pentest delivers shorter mean time to remediation and increased depth and breadth of coverage so you can focus on your mission of keeping attackers out and keeping IT/OT services running smoothly and securely.
Gartner says “Nation-state actors and criminal organizations operate with a level of sophistication that surpasses the preventative and detection capabilities of most security and risk management teams.”
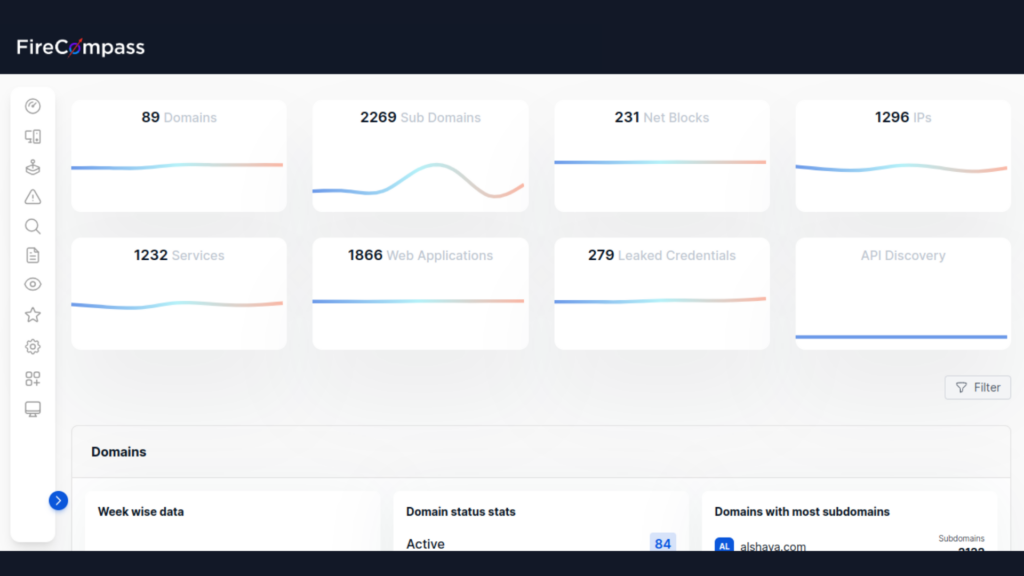
FireCompass runs continuously and indexes the deep, dark, and surface web using the same reconnaissance techniques as threat actors do & automatically discovers an organization's dynamic digital attack surface. Followed by active validation to eliminate false positives.
Identify critical risks in 24-72 hours with FireCompass. We use Multi-Stage Hunting Playbooks to conduct 30,000 attacks and checks on your Network, Web, Cloud, and other assets from our geographically distributed sensor network. Our Playbooks cover ransomware susceptibility, web app testing, credential stuffing, and attacker-style campaigns. We continuously test 100% of your assets to uncover all security risks.
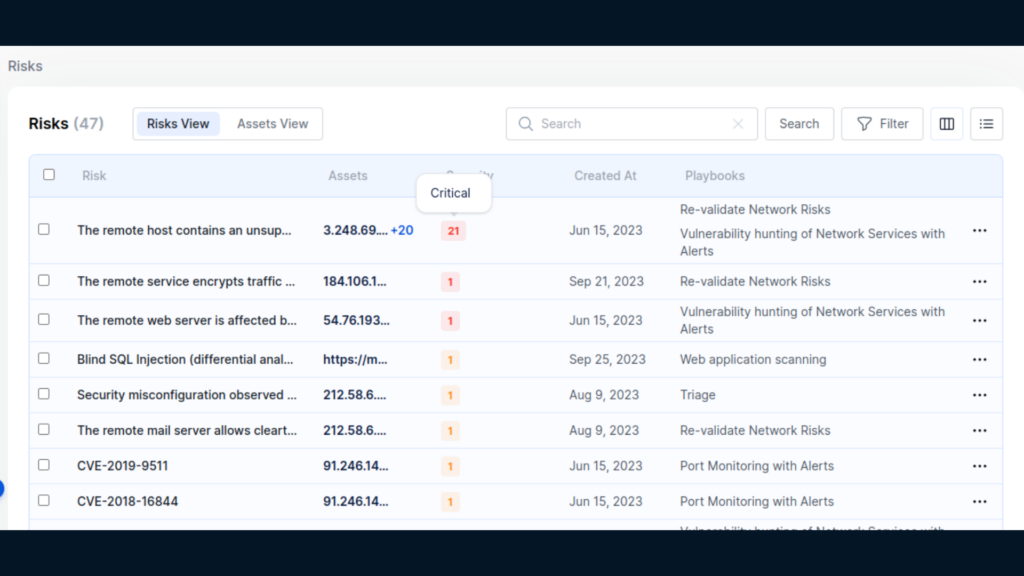
FireCompass Platform performs Recon, Hunting, Attack & Safe Exploitation on the attack surface. Attack & Safe Exploitation provide initial access point, exploitation proof of concepts (PoCs), Sample Data Exfiltration, C2 Agent Installation as some of the ways to validate the risk exploitability.
Failure to conduct frequent & extensive attacker-like reconnaissance leaves low-hanging fruits easily exploited by adversaries. The FireCompass platform works by doing:
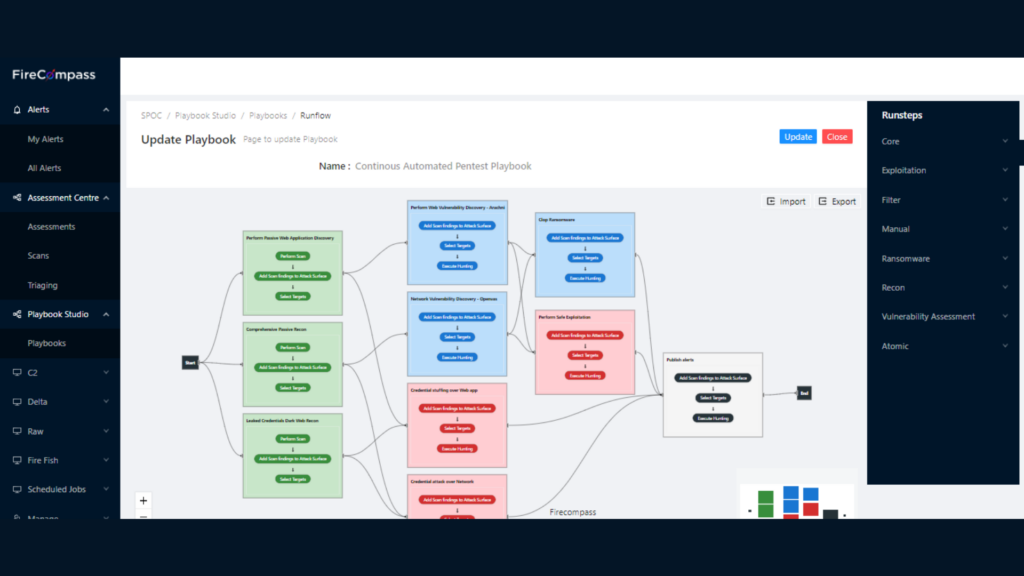
Find likely attack paths by emulating the most recent threat actors with a platform that never sleeps. Use ready-made playbooks to launch multi-stage attacks for ransomware susceptibility assessments, LOG4J, CISA Alerts for Known Exploited Vulnerabilities, critical infrastructure attacks, web application attacks, stolen credential attacks, social engineering attacks and more on every asset discovered in your digital surface to validate your security posture and accelerate risk mitigation. The FireCompass platform provides attack and hunting playbooks to:
FireCompass Platform performs Recon, Hunting, Attack & Safe Exploitation on the attack surface. Attack & Safe Exploitation uses initial access point, exploitation proof of concepts (PoCs), as some of the ways to validate the risk exploitability.
Conduct Pentest on 100% of Assets as compared to 20% of assets in traditional Pentest
Scale your pentesting to monthly frequency as compared to yearly traditional pentest
Identify most critical risks within 72 hours, and validate Security Controls at least monthly
Save upto 80% of your SecOps Bandwidth by Focusing on Prioritized Risks

We’ve put together some top talks from global security conferences that could help you get a hang on the debatable topic

We have listed a few breach response tactics that organizations need to keep handy for rainy days. Read to know more about how you can keep your organization safe.

Here we list 10 tools which can be used for Reconnaissance by Security teams in order to assess their own security posture against hackers.
Request Demo
You have successfully joined our subscriber list.
FireCompass – An EC Council Ecosystem Company.
©2025 . All Rights Reserved.