Discover Your 3rd/4th Party Risks Using Our Passive Recon. Use Our Active Pen Testing For Deeper 3rd Party Risk Assessments
Gartner predicts that by 2025, 45 percent of organizations worldwide will have experienced attacks on their software supply chains — a three-fold increase from 2021. The top three reasons organizations need to worry about supply chain risks are as follows:
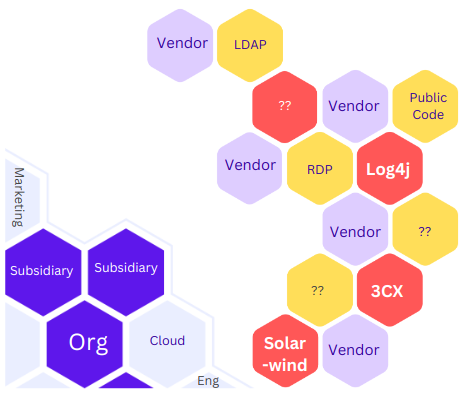
- Attacks such as SolarWinds, Log4j, 3CX, and others have impacted thousands of enterprises globally because of software supplied by third parties and vendors.
- U.S. government regulations mandate that U.S. organizations create and maintain SBOMs (Software Bill of Materials).
- Third parties can also expose data, vulnerable servers, and Shadow IT, resulting in breaches that can impact your organizations.
Single Platform For Continuous Recon, Risk Hunting and Attack Emulation
How FireCompass Helps
Discover Vendors & Generate Software Bill of Material
FireCompass Recon Platform sends continuous probes, grab banners, and discover various 3rd party software, vendors and subsidiaries. The platform also fingerprint the services and perform contextual attribution to identify assets related to your 3rd / 4th Parties. It can generate Software Bill of Material consisting of 3rd party software you are using, their versions, and Banners.
Vendor’s Passive Security Posture
FireCompass Platform indexes 3rd Parties Domains, Subdomains, Ips, Services, Service Banners, Web App Pages and Public Code in a searchable Gigantic Graph of Entities and Relations. It helps the platform to identify, correlate and identify all possible passive risks based on the services, banners and fingerprinting results. The platform assigns various risk scores to provide overall security posture of your vendors.
Automated
Pentesting
FireCompass Platform validates the risks and security controls by launching various safe attacks & exploits on the exposed attack surface. The Platform has various adversary emulation playbooks based on the industry and threat Intelligence. Adversary emulation uses multi stage attack trees to orchestrate attacks, and validate exploitability and security controls
Discover Vendors & Generate Software Bill of Material
The FireCompass platform leverages advanced attribution techniques across the deep, dark, and surface web to uncover assets associated with your 3rd/4th Party Vendors and Subsidiaries.
With the FireCompass Recon Platform, you can achieve the following:
- Discover who your vendors, subsidiaries, and open-source software providers are.
- Establish an asset inventory for compliance and testing purposes.
- Uncover and address Shadow IT instances, including exposed Public Cloud Buckets and RDP, as well as other vital services.
- Generate a comprehensive Software Bill of Materials (SBOM) that outlines the vendors, versions, technologies, and banners associated with your assets.
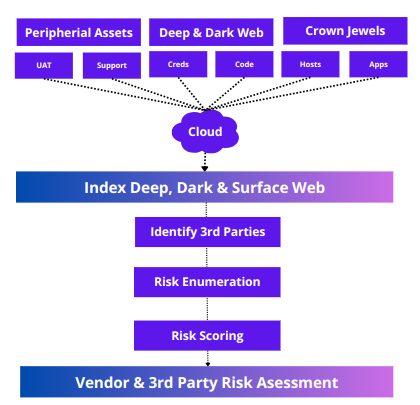
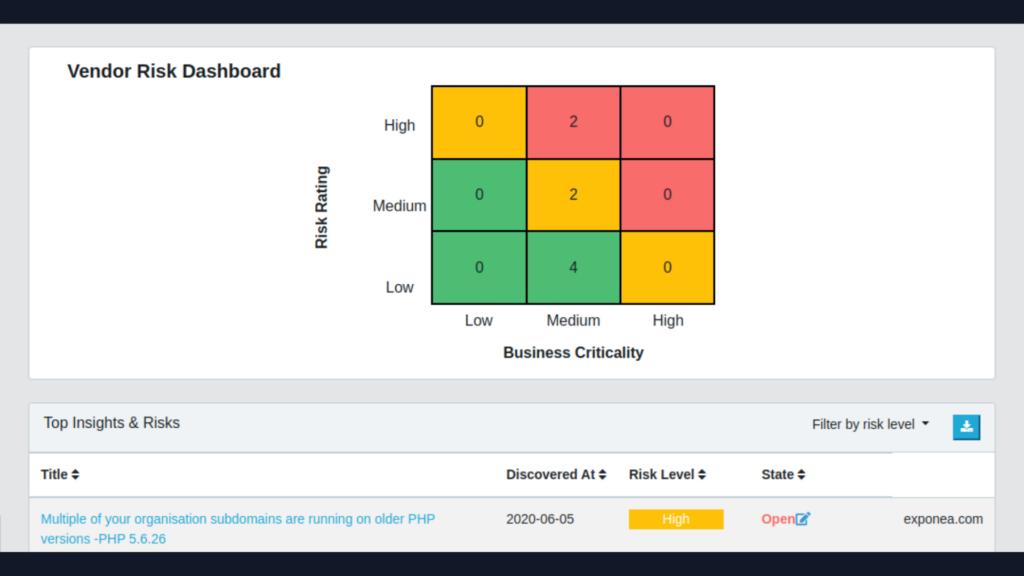
Vendor’s Passive Security Posture
The FireCompass Platform offers the most updated Vendor Security Posture dashboard as a strategic tool that passively collects data, matching it against a comprehensive risk database to identify and expose potential security risks. It assigns an overall risk score to each vendor, enabling the following capabilities:
- Provides real-time visibility into the security posture of your vendors.
- Allows for the evaluation of vendors based on their current security measures.
- Sends alerts to vendors about critical security issues needing immediate attention.
- Supports annual vendor assessment practices, enhancing due diligence and risk management.
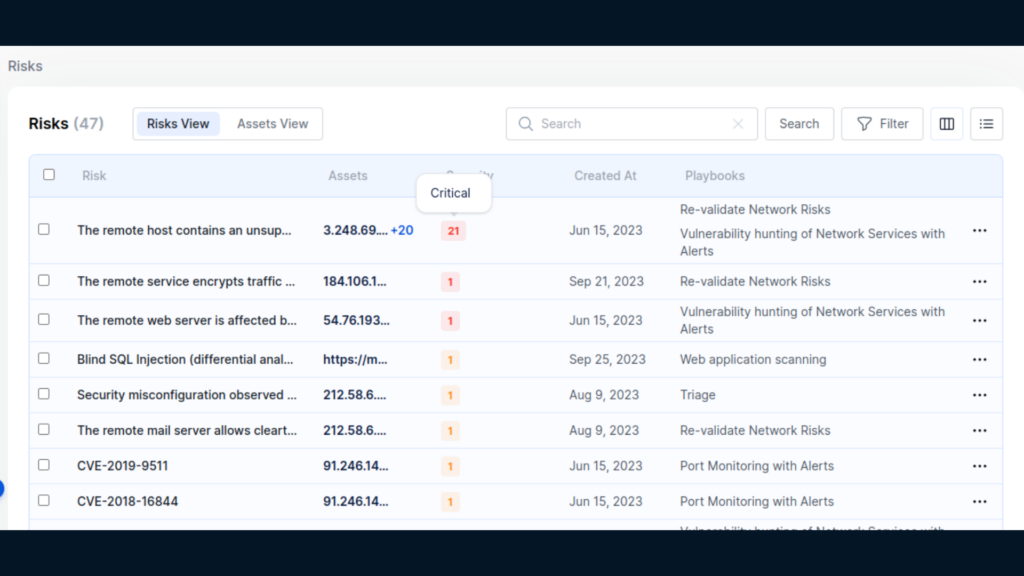
Automated Pentesting
FireCompass platform offers the ability to conduct active testing on your vendors to obtain the most realistic security posture of your exposed attack surface. The platform launches safe and curated tests on your vendor’s attack surface, providing validated risks and reducing false positives by 95%. With the FireCompass Automated Pentesting platform, you can:
- Perform deeper testing of your most critical vendors, third parties, and subsidiaries.
- Enforce stringent security practices with your third parties.
- Mitigate any critical risks that can impact your organization from third parties.
- Incorporate more accurate third-party risks into your Risk Register.
Benefits of Using FireCompass
2x
Accurate SBOM
Generate Accurate SBOM more accurate than any other tool
95%
Accurate Risks
Automated Pentesting can help you reduce false positives by 95%
80%
Cost Saving
Save upto 80% of your SecOps Bandwidth by Focusing on Prioritized Risks
50x Reduction of Risk Window
Identify most critical risks within 72 hours, and validate Security Controls at least monthly
Frequently Asked Questions
How does Automated Red Teaming differ from Manual Red Teaming and Penetration Testing?
What are the benefits of Automated Red Teaming with FireCompass?
- • Increased Efficiency: FireCompass’ automated processes can help streamline your red teaming efforts and maximize your team’s efficiency. FireCompass can automate tasks such as assessment scoping, data collection, data analysis, prioritization, and reporting, allowing your team to focus on the more important aspects of red teaming and blue teaming.
- • Improved Coverage: FireCompass’ automated red teaming tools can provide comprehensive coverage of your IT environment. By automating the data collection and analysis process, FireCompass can help you identify threats and vulnerabilities more quickly across your entire IT infrastructure.
- • Enhanced Visibility: FireCompass’ automated tools can provide detailed visibility into your IT environment. Automated data collection and analysis can give you a more comprehensive view of your IT infrastructure, allowing you to identify potential threats and vulnerabilities more quickly.
- • Reduced Costs: Automated red teaming with FireCompass can help reduce costs by eliminating the need to hire and train additional personnel. Automation can also help reduce the time and effort required for manual tasks, resulting in significant cost savings.
How does FireCompass automate Red Teaming?
Where does Automated Red Teaming improve compliance?
How does Automated Red Teaming improve Blue Teaming?
What are the common tools and techniques used in Red Teaming?
- • Vulnerability Scanning: Using automated tools to identify and report on potential security weaknesses in your network and systems.
- • Social Engineering: Manipulating people into giving up confidential information or performing unauthorized actions.
- • Network Mapping: Utilizing tools to map out a network’s topology and identify potential entry points.
- • Penetration Testing: Using automated tools and manual methods to identify and exploit weaknesses in your networks and systems.
- • Physical Security Testing: Utilizing physical reconnaissance and covert methods to assess the physical security of your organization.
- • Malware Analysis: Examining malicious code to better understand the nature and purpose of the attack.
- • Database Enumeration: Utilizing tools to identify and retrieve information from databases.
- • Application Security Testing: Utilizing tools to evaluate the security of web and mobile applications.
- • Wireless Network Testing: Utilizing tools to assess the security of wireless networks.
- • Phishing Campaigns: Utilize emails to employees or partners to gain initial access or information about systems including credentials.
How does FireCompass eliminate false positives?
Important Resources

We’ve put together some top talks from global security conferences that could help you get a hang on the debatable topic

We have listed a few breach response tactics that organizations need to keep handy for rainy days. Read to know more about how you can keep your organization safe.
Read More

Here we list 10 tools which can be used for Reconnaissance by Security teams in order to assess their own security posture against hackers.
About FireCompass
FireCompass is a SaaS platform for Continuous Automated Red Teaming (CART) and External Attack Surface Management (EASM) that acts as an integral part of a good exposure management program.
- Single Platform for Attack Surface Management and Automated Penetration Testing & Red Team
- Daily Risk Port Scanning & Adversary Emulation through multiple Attack Playbooks
- Prioritized Risks with real-time alerts for faster detection and remediation
Request Demo
Thank you!
You have successfully joined our subscriber list.

