Fortnightly Critical Vulnerabilities: February Part 1
The FireCompass research team identified a huge number of CVEs that are high in severity and ransomware, botnets, and threat actors creating Havoc. Some of the CVEs identified are of popular commercial products used by various industries and some new & well-known malware targeting industries for this week. In this, we will list important CVEs discovered as well as the list of malware, threat actors and botnets which were most active along with the CVEs that they were using in their campaigns.
List of Critical Vulnerabilities That Were Exploited – FireCompass Research :
- CVE-2020-12812, CVE-2024-21762 – FortiOS Multiple Vulnerability
- CVE-2020-0688, CVE-2021-34523, CVE-2024-21410 – Microsoft Exchange Multiple Vulnerability
- CVE-2021-21972 – vSphere Client
- CVE-2023-35188 – SolarWinds Platform
- CVE-2024-21364, CVE-2024-21376, CVE-2024-20667 – Microsoft Azure Multiple Vulnerability
- CVE-2024-21413, CVE-2024-21378 – Microsoft Outlook Multiple Vulnerability
- CVE-2023-51072 – NOC-Nagios XI
- CVE-2023-32328, CVE-2023-32330, CVE-2023-43017 – IBM Security Verify Access Multiple Vulnerability
- CVE-2023-39297, CVE-2023-45025, CVE-2023-47568 – QNAP OS Multiple Vulnerability
- CVE-2024-20252, CVE-2024-20254, CVE-2024-20255 – Cisco Expressway Series and Cisco TelePresence Video Communication Server (VCS) Multiple Vulnerability
- CVE-2024-0338 – XAMPP
- CVE-2024-0253, CVE-2024-0269 – ManageEngine ADAudit Plus Multiple Vulnerability
List of Malwares And Threat Actors:
- CVE-2022-42475 – FortiOS SSL-VPN
- CVE-2023-36025 – Microsoft Windows and Windows Server
Detailed Analysis: Vulnerabilities
CVE-2020-12812, CVE-2024-21762 – FortiOS Multiple Vulnerability:
CVE-2020-12812
CVE-2020-12812 is a vulnerability in FortiOS SSL VPN that allows users to bypass two-factor authentication (2FA) by simply changing the case of their username. This vulnerability exists because of inconsistent case-sensitivity handling between local and remote authentication methods. For example, if a user’s username is stored in lowercase on the local system but uppercase on the remote authentication server, they can bypass 2FA by logging in with a mixed-case username (e.g., “jUsEr” instead of “user”). This vulnerability affects FortiOS versions 6.4.0, 6.2.0 to 6.2.3, and 6.0.9 and below. It is recommended to upgrade to FortiOS 6.4.1 or later, 6.2.4 or later, or 6.0.10 or later to address this vulnerability.
CVE-2024-21762
CVE-2024-21762 is a critical vulnerability in Fortinet FortiOS and FortiProxy software that exposes devices to attackers. This vulnerability, caused by an out-of-bounds write issue, allows attackers to remotely execute arbitrary code or commands on affected devices by sending specially crafted requests. This means attackers could potentially take full control of your device and use it for malicious purposes. If you use Fortinet FortiOS or FortiProxy, it’s crucial to update to the latest patched version immediately to address this vulnerability and protect your devices.
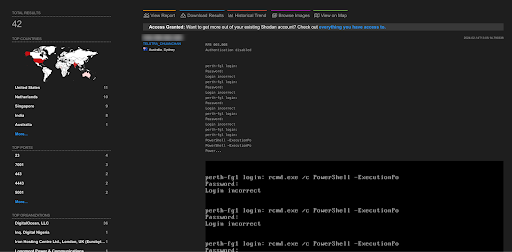
A total of 42 endpoints of FortiOS are exposed on the Shodan.
CVE-2021-21972 – vSphere Client
A critical vulnerability in VMware vCenter Server (versions 7.x before 7.0 U1c, 6.7 before 6.7 U3l, and 6.5 before 6.5 U3n) and VMware Cloud Foundation (versions 4.x before 4.2 and 3.x before 3.10.1.2) allows remote attackers with network access to port 443 to execute arbitrary code with unrestricted privileges on the underlying operating system. This vulnerability exists due to an unauthenticated remote code execution flaw within a vCenter Server plugin.
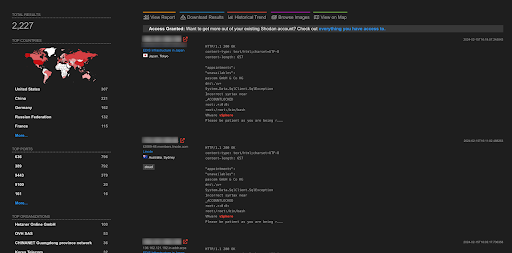
A total of more than 2K endpoints of vSphare are exposed on the Shodan.
CVE-2023-35188 – SolarWinds Platform
CVE-2023-35188 exposes a critical security risk in SolarWinds Platform versions up to 2023.4.2. It allows attackers to remotely execute malicious code within the platform if they have valid user credentials. This vulnerability arises from a flaw in how the platform handles SQL statements, specifically within the “create” function. While user authentication is required for exploitation, attackers could potentially leverage stolen credentials or social engineering tactics to gain access. Upgrading to the latest SolarWinds Platform version (2023.4.3 or later) is essential to mitigate this risk.
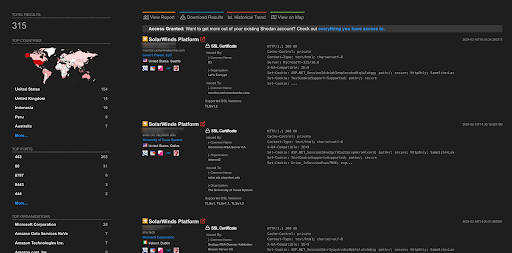
A total of 315 endpoints of SolarWinds Platform are exposed on the Shodan.
CVE-2024-21364, CVE-2024-21376, CVE-2024-20667 – Microsoft Azure Multiple Vulnerability:
CVE-2024-21364
CVE-2024-21364 is a recently discovered critical vulnerability in Microsoft Azure Site Recovery that allows attackers to escalate their privileges on the system. While specific details of the exploit are still emerging, it’s crucial to prioritize patching your Azure Site Recovery instance immediately to prevent potential compromise.
CVE-2024-21376
CVE-2024-21376 is a critical vulnerability in Microsoft Azure Kubernetes Service (AKS) affecting Confidential Containers (AKSCC). It allows attackers to remotely execute malicious code within AKS, potentially granting them unrestricted access to sensitive data and resources. This vulnerability arises due to improper isolation between untrusted AKS nodes and AKSCC, enabling attackers to exploit specific configurations and gain control over confidential guests and containers. The vulnerability requires no authentication and carries a CVSSv3 score of 9.0, indicating a severe risk. Microsoft has released security patches, and immediate patching is crucial to mitigate this vulnerability.
CVE-2024-20667
A critical vulnerability (CVE-2024-20667) exists in Azure DevOps Server versions 2019.1.2, 2020.1.2, and 2022.1, allowing attackers to remotely execute malicious code on affected servers. This vulnerability, categorized as “remote code execution,” grants attackers complete control over the server, enabling them to steal sensitive data, disrupt operations, or install malware.The vulnerability stems from an issue with how the server processes specific requests. Exploiting this vulnerability requires no user interaction or authentication, making it highly dangerous.
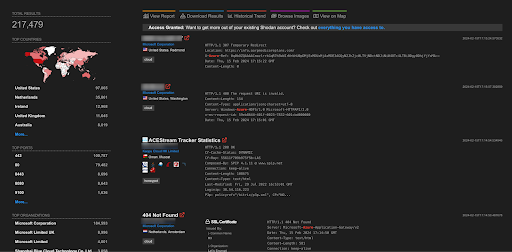
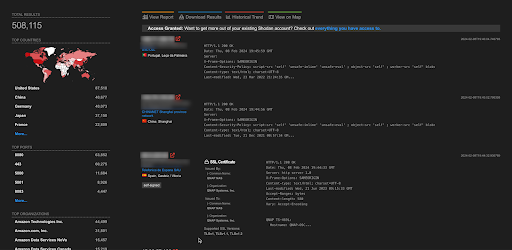
A total of more than 217K endpoints of Azure are exposed on the Shodan.
CVE-2024-21413, CVE-2024-21378 – Microsoft Outlook Multiple Vulnerability:
CVE-2024-21413
CVE-2024-21413 is a critical remote code execution vulnerability affecting Microsoft Outlook versions included in Microsoft Office 2019, Microsoft 365 Apps for Enterprise, Microsoft Office LTSC 2021, and Microsoft Office 2016. It allows attackers to gain high privileges on a vulnerable system, potentially leading to data theft, malware installation, or complete system compromise.The vulnerability arises from a flaw in how Outlook handles malicious links that bypass the Protected View Protocol. This enables attackers to leak local NTLM credential information and ultimately achieve remote code execution (RCE) without requiring any user interaction or specific privileges.
CVE-2024-21378
A critical vulnerability (CVE-2024-21378) exists in Microsoft Outlook, potentially affecting various versions within Microsoft Office suites (2019, 365 Apps, LTSC 2021, 2016). This vulnerability allows attackers to remotely execute malicious code on your system, granting them complete control and potentially leading to data breaches, malware installation, or system disruption.
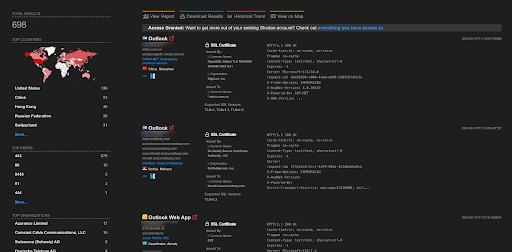
A total of 698 endpoints of Microsoft Outlook are exposed on the Shodan.
CVE-2023-51072 – NOC-Nagios XI
Nagios XI versions up to 2024R1 contain an XSS vulnerability where low-privileged users can upload audio files laced with malicious code. This code silently executes for any user viewing the file, potentially granting attackers complete control over accounts, data, and even the entire system. Upgrade immediately to version 2024R1.0.1 or later, disable audio uploads if unused, and educate users to avoid falling victim. Remember, vigilance and ongoing security measures are crucial for complete protection.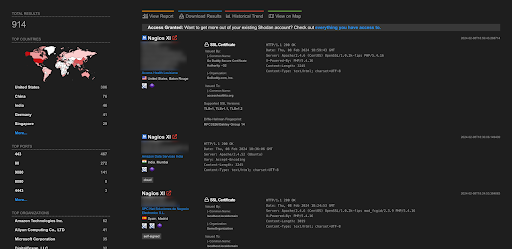
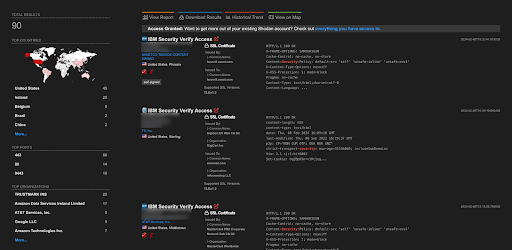
CVE-2023-32328, CVE-2023-32330, CVE-2023-43017 – IBM Security Verify Access Multiple Vulnerability
CVE-2023-32328
IBM Security Verify Access versions up to 10.0.6.1 are vulnerable due to insecure communication protocols, potentially allowing attackers on the network to gain complete control of the server. This critical vulnerability (CVE-2023-32328) exposes sensitive information and lacks a publicly available exploit yet. Update immediately to a patched version (10.0.7 or later) to mitigate the risk. Remember, swift action and vigilance are key to protecting your systems.
CVE-2023-32330
CVE-2023-32330 exposes a critical vulnerability in IBM Security Verify Access 10.0.0.0 to 10.0.6.1, where insecure calls within the system could grant attackers on the network complete control of the server. This vulnerability (IBM X-Force ID: 254977) poses a severe risk as it lacks a public exploit yet. Immediate patching to version 10.0.7 or later is essential to safeguard your system and sensitive data. Remember, staying ahead of vulnerabilities through timely updates and proactive security measures is crucial.
CVE-2023-43017
A critical vulnerability (CVE-2023-43017) exists in IBM Security Verify Access versions 10.0.0.0 to 10.0.6.1. Privileged users with malicious intent can exploit this flaw to install a configuration file enabling remote access, potentially compromising confidentiality, integrity, and availability of the system. While technical details are limited, immediate patching to version 10.0.7 or later is essential to address this high-risk vulnerability. Remember, staying informed and proactive with security updates is crucial for optimal protection.
CVE-2023-39297, CVE-2023-45025, CVE-2023-47568 – QNAP OS Multiple Vulnerability
CVE-2023-39297
Several QNAP operating systems are vulnerable to CVE-2023-39297, an OS command injection flaw allowing authenticated users to execute malicious commands remotely. Update immediately to QTS 5.1.4.2596 (build 20231128) or later, QTS 4.5.4.2627 (build 20231225) or later, QuTS hero h5.1.4.2596 (build 20231128) or later, QuTS hero h4.5.4.2626 (build 20231225) or later, or QuTScloud c5.1.5.2651 or later to prevent attackers from potentially taking control of your system.
CVE-2023-45025
QNAP operating systems before QTS 5.1.4.2596 (build 20231128), QTS 4.5.4.2627 (build 20231225), QuTS hero h5.1.4.2596 (build 20231128), QuTS hero h4.5.4.2626 (build 20231225), and QuTScloud c5.1.5.2651 are vulnerable to CVE-2023-45025, an OS command injection flaw. This vulnerability allows malicious users to execute commands on your system over the network, potentially granting them complete control. Update immediately to the mentioned versions or later to mitigate the risk.
CVE-2023-47568
QNAP operating systems before QTS 5.1.5.2645 (build 20240116), QTS 4.5.4.2627 (build 20231225), QuTS hero h5.1.5.2647 (build 20240118), QuTS hero h4.5.4.2626 (build 20231225), and QuTScloud c5.1.5.2651 are vulnerable to CVE-2023-47568. This SQL injection flaw lets authenticated users inject malicious code over the network, potentially compromising your system. Update immediately to the mentioned versions or later to secure your QNAP device.
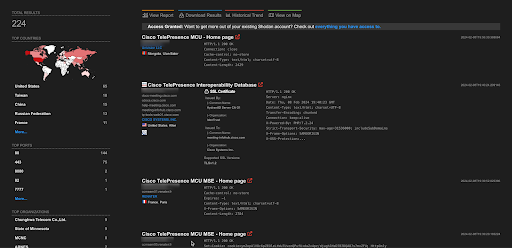
CVE-2024-20252, CVE-2024-20254, CVE-2024-20255 – Cisco Expressway Series and Cisco TelePresence Video Communication Server (VCS) Multiple Vulnerability
CVE-2024-20252
Unpatched Cisco Expressway Series and TelePresence VCS devices (up to a specific date) are vulnerable to multiple CSRF attacks, allowing unauthenticated remote attackers to manipulate the system and potentially gain control. These critical vulnerabilities require immediate patching to Cisco Expressway Control (Expressway-C) or Edge (Expressway-E) devices and TelePresence VCS servers to prevent attackers from exploiting them.
CVE-2024-20254
Unpatched Cisco Expressway and TelePresence VCS devices (up to a specific date) are susceptible to various CSRF attacks, enabling unauthenticated remote attackers to execute arbitrary actions and potentially take control of the system. These critical vulnerabilities demand immediate patching of both Cisco Expressway Control/Edge devices and TelePresence VCS servers to prevent exploitation.
CVE-2024-20255
An unpatched Cisco Expressway Series or TelePresence VCS server harbours a CSRF vulnerability in its SOAP API. This means a remote attacker, without needing any prior authentication, can trick a user with access to the REST API into clicking a malicious link. If successful, the attacker can force the affected system to reload, potentially disrupting operations or setting the stage for further attacks. Immediate patching is crucial to close this security gap.
CVE-2024-0338 – XAMPP
XAMPP versions up to 8.2.4 are vulnerable to an exploit (CVE-2024-0338) where attackers can inject malicious code through a long file debug argument. This code gives them full control of the system, allowing them to steal data, install malware, or disrupt operations. Upgrade to XAMPP version 8.2.5 or later immediately to prevent attackers from exploiting this critical vulnerability.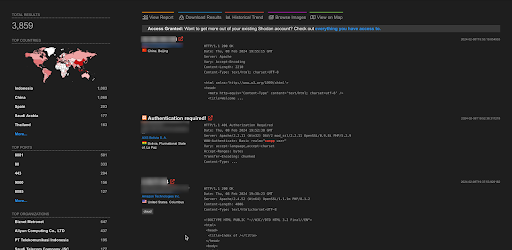
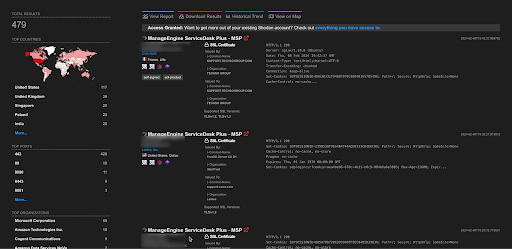
CVE-2024-0253, CVE-2024-0269 – ManageEngine ADAudit Plus Multiple Vulnerability
CVE-2024-0253
ManageEngine ADAudit Plus versions 7270 and below contain a critical vulnerability (CVE-2024-0253) that allows authenticated attackers to inject malicious SQL code. This could grant them complete control over the system, compromising sensitive data and disrupting operations. Upgrade to version 7271 or later immediately to address this vulnerability.
CVE-2024-0269
ManageEngine ADAudit Plus versions 7270 and below are susceptible to an authenticated SQL injection vulnerability (CVE-2024-0269) within the File-Summary DrillDown feature. This allows attackers with valid access to inject malicious code and potentially compromise the entire system. Thankfully, a fix is available in version 7271, so upgrading immediately is crucial to safeguard your data and infrastructure.
Important Weekly Threat Actors
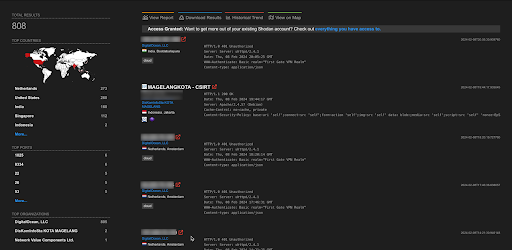
CVE-2022-42475 – FortiOS SSL-VPN
A Chinese cyber-espionage group exploited the CVE-2022-42475 FortiOS SSL-VPN vulnerability to compromise FortiGate firewalls at the Dutch Ministry of Defence. They deployed a persistent RAT malware named Coathanger, designed to steal data and potentially gain control of the system. This malware is stealthy and survives reboots and firmware upgrades. Dutch intelligence linked the attack with high confidence to a Chinese state-sponsored hacking group, highlighting the dangers of unpatched vulnerabilities and the sophisticated tactics employed by such actors.
CVE-2023-36025 – Microsoft Windows and Windows Server
CVE-2023-36025 was exploited by attackers wielding a new variant of Mispadu Stealer, a Delphi-based malware targeting Latin America, particularly Mexico. This malware, linked to a broader banking malware family, spread via phishing emails containing URLs that bypassed SmartScreen warnings using CVE-2023-36025. The attackers are unknown, but the malware’s characteristics suggest connections to a Mispadu sample from earlier in 2023. This incident highlights the evolving tactics of cybercriminals and the need for proactive defence measures against constantly developing malware threats.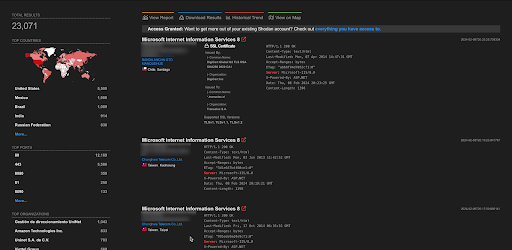
Blog By
Author: Debdipta Halder
Assisted By: Soumyanil Biswas, Faran Siddiqui, Anirban Bain
About FireCompass:
FireCompass is a SaaS platform for Continuous Automated Pen Testing, Red Teaming and External Attack Surface Management (EASM). FireCompass continuously indexes and monitors the deep, dark and surface webs using nation-state grade reconnaissance techniques. The platform automatically discovers an organization’s digital attack surface and launches multi-stage safe attacks, mimicking a real attacker, to help identify breach and attack paths that are otherwise missed out by conventional tools.
Feel free to get in touch with us to get a better view of your attack surface.