Top 10 Pen Testing Tools in 2024
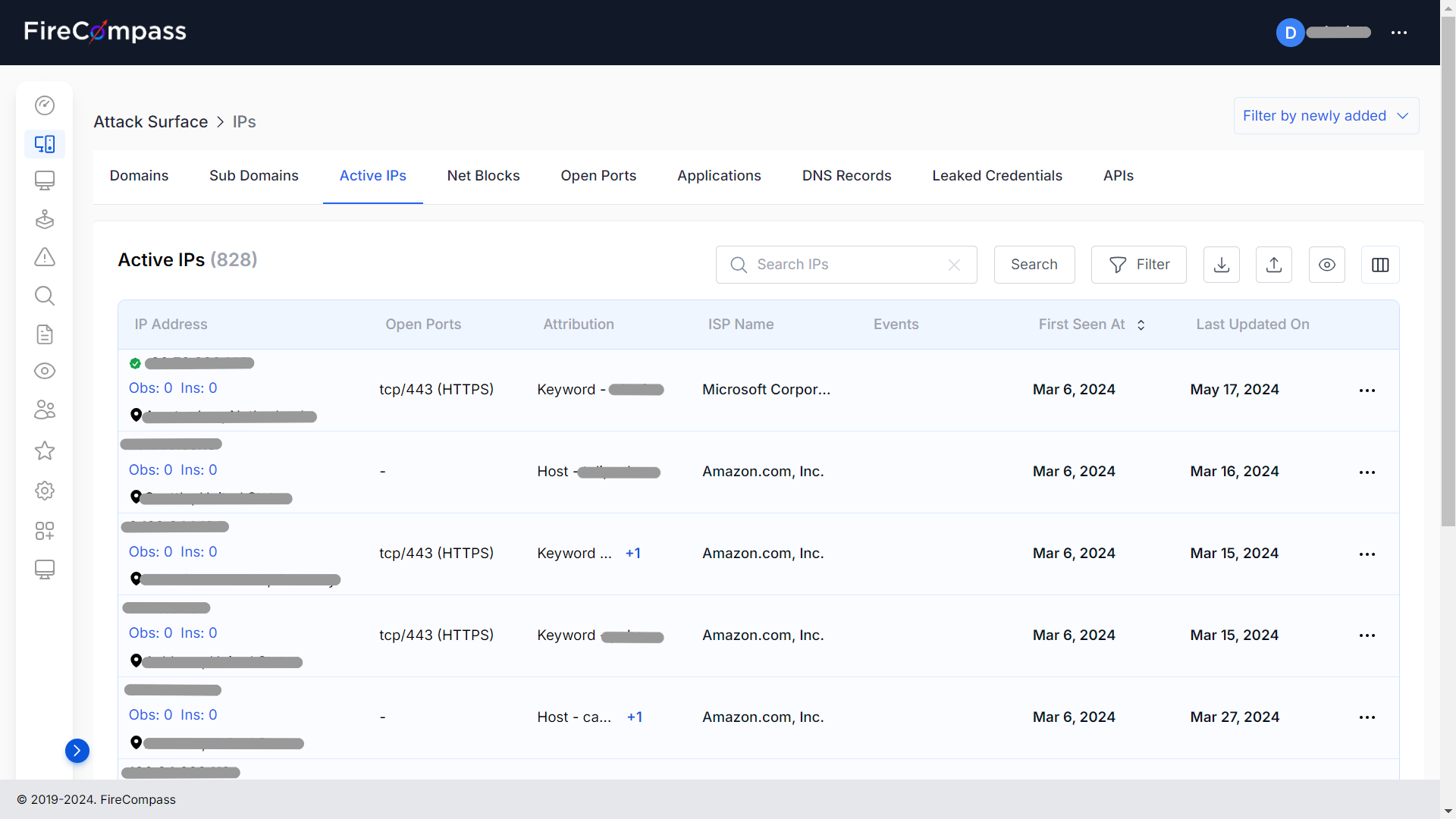
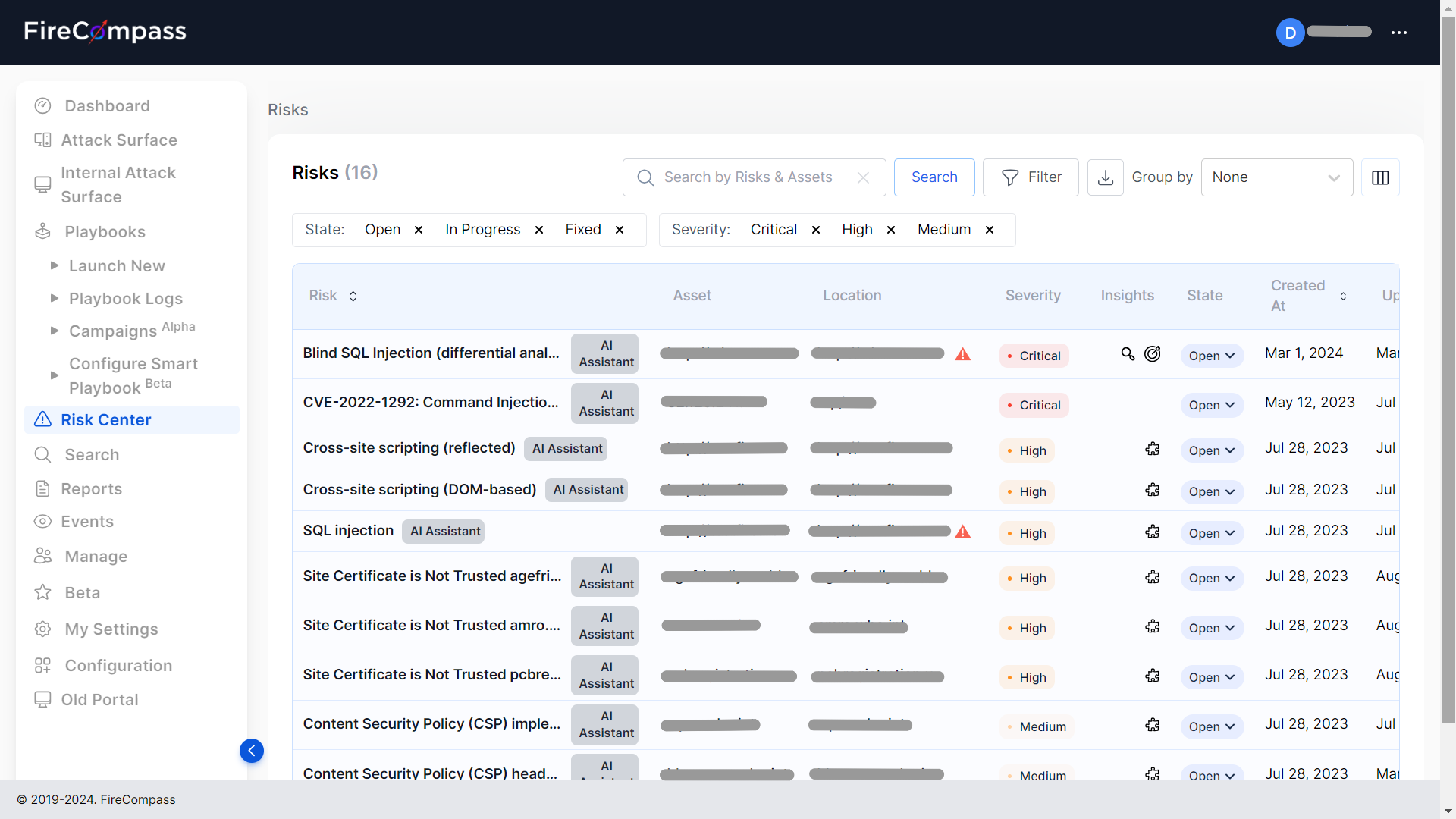
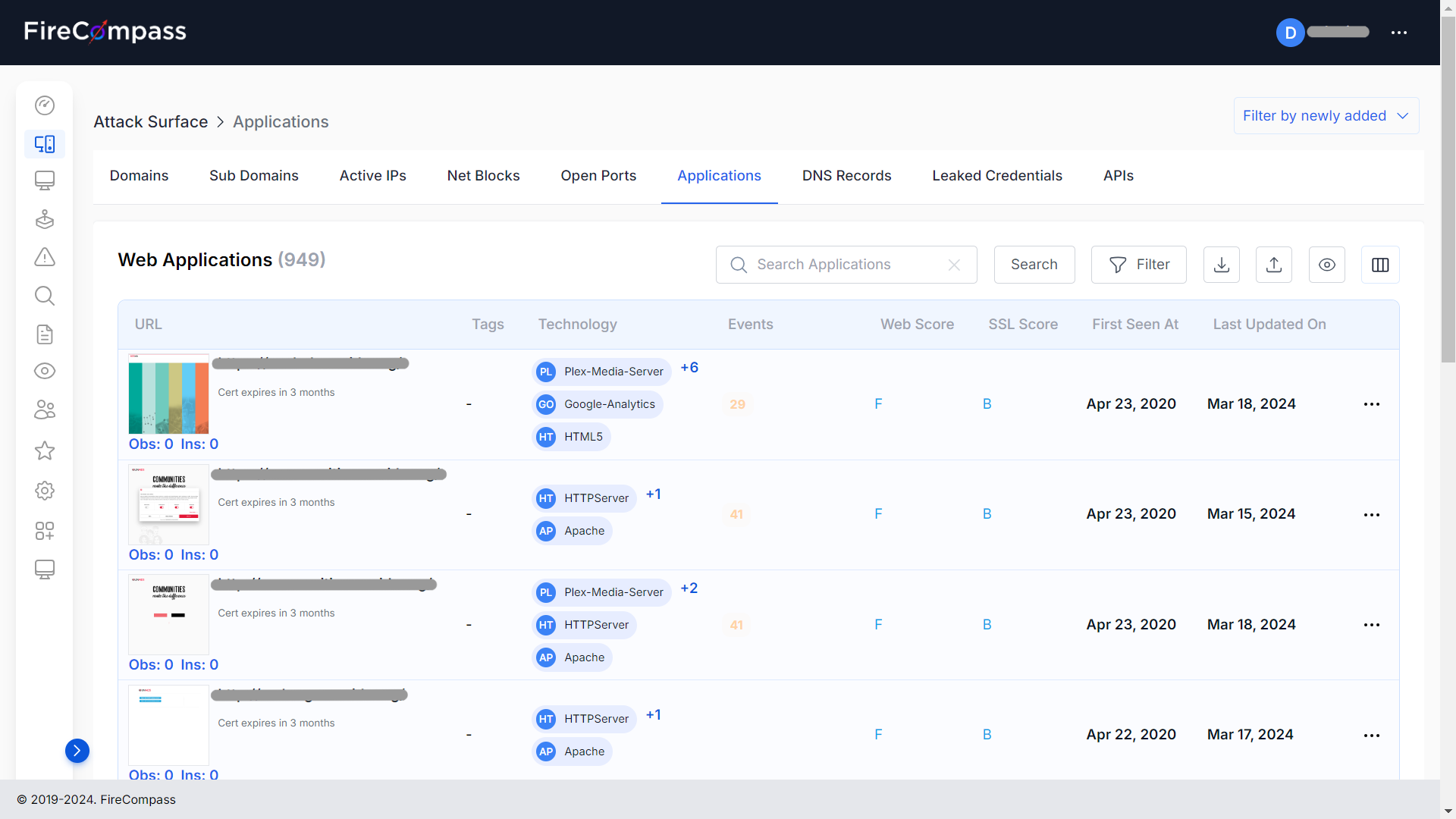
Top 10 Pen Testing Tools in 2024 Penetration testing, commonly known as PenTesting, is a method used by cybersecurity professionals to evaluate the security of a system or network by simulating attacks. This approach helps organizations identify weaknesses that could be exploited by malicious hackers. In 2024, several tools have emerged that stand out for… Read More »Top 10 Pen Testing Tools in 2024